Learn About Using the VPN Pros And Cons
Welcome to this page which is devoted to outlining the VPN pros, as well as the main differences between VPN and VPN proxy servers! We encourage you to take the time and get familiar with this content – it can help you get clear why to consider using a VPN in the first place, what you can expect from the service and why it is not accurate to use VPN service and VPN proxy service in an interchangeable way. Enjoy!
What is a VPN and Why You Need One
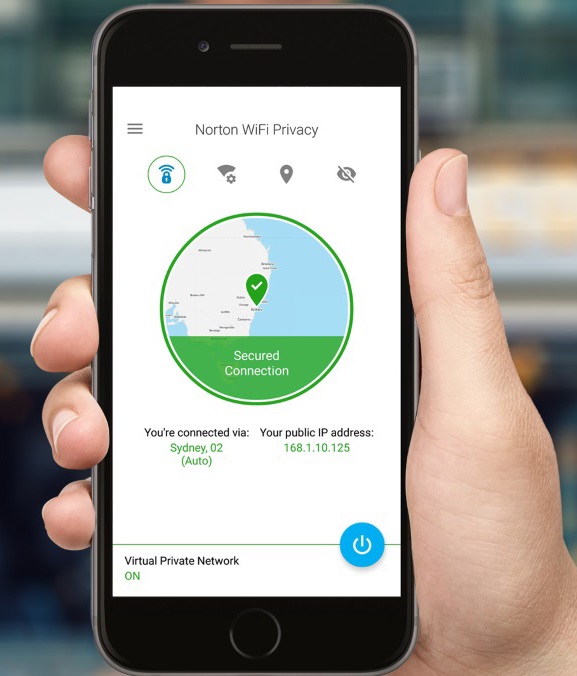
As we already mentioned, VPN stands for virtual private network or a service, thanks to which you can benefit from a higher privacy and security and at the same time get your work done online. What makes VPN-s so popular and valuable both for business and private purposes, has to do with the fact that using VPN pros enables business users to safely access work networks from outside their offices, while personal users can protect themselves against rogue system administrators who might be willing to misuse their personal information.
It is not a secret that public Wi-Fi hotspots are not secure because anyone can access them and in the same time it doesn’t take a lot for people to check what others are doing online, as well. In comparison to them, using LAN-s provides you with a little bit more security. However, it is not considered to be enough when it comes to business context. In this case, there are additional measures to be implemented, such as dedicated firewall appliances, IT staff trained in security practices, etc.
 Quite a long time ago, it was not uncommon for companies to install a leased communications line from a provider like a T-1 or ISND line. In this way, they were capable of using a secured private tunnel between two points. Even if this might have contributed to increasing security, we cannot underestimate the fact that using VPN pros is much more cost-effective. Having in mind that a VPN serves as a tunnel between a device (PC, laptop, phone, etc.) and a LAN, it still uses the open Internet, but at the same time, the connection is much more secure thanks to the encryption. So it is not only harder to break in, but even if someone succeeds in doing so, the traffic packets are gibberish when examined.
Quite a long time ago, it was not uncommon for companies to install a leased communications line from a provider like a T-1 or ISND line. In this way, they were capable of using a secured private tunnel between two points. Even if this might have contributed to increasing security, we cannot underestimate the fact that using VPN pros is much more cost-effective. Having in mind that a VPN serves as a tunnel between a device (PC, laptop, phone, etc.) and a LAN, it still uses the open Internet, but at the same time, the connection is much more secure thanks to the encryption. So it is not only harder to break in, but even if someone succeeds in doing so, the traffic packets are gibberish when examined.
What is more, your IP address gets replaced by an intermediary VPN service as a result of manipulating the header information in the packet stream. So, this means that it will seem as if you were currently in a neighbor country if your VPN server happens to be situated there. Spoofing your location might be extremely useful sometimes. Let us explore the following example. You come to know that there is a company employing people who only live in another country. Until you manage to move there, it might be helpful to be able to send an email from the address of a friend who lives there, right? Also, it is not uncommon for users to get around regional DRM restrictions for streaming content exactly by benefiting from a VPN. What is more, VPN-s might be the only chance for people who live in countries with high censoring and monitoring like China to be able to communicate with the outer world. Even if all these scenarios are associated with risk and being illegal, it is not hard to imagine what might drive people to act that way, isn’t it?
Legislation
Still, keep in mind that using VPN pros doesn’t need to be considered not legitimate all the time. There are cases where this is not necessarily the case. First, imagine what it would be like for you to be a college student who needs to access the school’s costly subscription databases in a secure way. Second, what about downloading legal content by using BitTorrent? It is understandable why most of us wouldn’t be willing to risk getting accused of downloading something we may not have aimed at in the first place. The third scenario relates, especially to Americans. It is quite often for US citizens to have signed up for a paid music or video streaming service and then not be able to access 100% of the content while being abroad. Even if providers like Netflix are more and more looking for ways to avoid geoblocking workarounds, using a VPN is still an option. Last, but not least, let us also mention that people often decide to purchase a VPN service because they would like to make sure that their right to keep their information private is ensured.
VPN Pros Summary
So, after we have gained an idea what kind of “good” and “evil” purposes people can use VPN-s for, let us summarize the benefits in a systematic way:
- Enjoying security to unsecured connection – Whoever had faced a situation when he or she needed to connect their device to a public Wi-Fi hotspot needs to keep in mind that this “practice” is associated with significant risks when it comes to your data. Therefore, you might be willing to consider using a virtual private network which can help you both send and receive information in a much more secure way.
- Getting around blocked sites – This is definitely another juicy benefit of using VPN pros especially as far as sites blocked on a specific network are concerned. For instance, there are a lot of companies or colleges that find blocking social media related sites necessary in order to avoid having to deal with users who access them. Virtual private networks enable you to get around these restrictions and still be able to enjoy your preferred sites on such connections.
 Benefitting from higher anonymity – Whether you are aware of it or not, it doesn’t take a lot of time or efforts to manage to track files that someone has accessed or downloaded on the Internet by using their IP address. You didn’t know about that? Don’t worry. There are ways in which you can prevent this from happening to you. And using a VPN connection is one of them. So, consider providing yourself with such a service if you happen to be willing to download and share legally obtained files with friends and family members without worrying about your IP address. VPN’s security protocols contribute to keeping it hidden.
Benefitting from higher anonymity – Whether you are aware of it or not, it doesn’t take a lot of time or efforts to manage to track files that someone has accessed or downloaded on the Internet by using their IP address. You didn’t know about that? Don’t worry. There are ways in which you can prevent this from happening to you. And using a VPN connection is one of them. So, consider providing yourself with such a service if you happen to be willing to download and share legally obtained files with friends and family members without worrying about your IP address. VPN’s security protocols contribute to keeping it hidden.- Getting censorship decreased – This benefit particularly applies to people who happen to live or temporally be in a country where the government blocked certain websites from being accessed (such as China). Having to deal with increased monitoring and censorship might be really challenging, so in these cases, it is not uncommon for VPN pros to be considered an incredibly valuable ally in the process of getting around such restrictions.
- Enjoying full privacy when browsing – There a lot of people who are surprised to find out that it is not uncommon for search engines like Google to log data so that when you type it later it comes back in the original format. VPN-s can also be used as a way of preventing search history from remaining attached to your PC’s IP address.
- Networking different business locations together – Networking various business locations together comes in handy especially for large businesses with multiple locations (often technically-based). They use virtual private networks in order to be able to benefit from one unified connection between all facilities. This means that it is the VPN pros that connect the separate entities all across the city, the state, the country or even the world.
- Getting your data easily encrypted – If you are willing to get your data encrypted before you send it online without having to invest a lot of time and effort, then a VPN service might be worth taking a look at. In this way, you will be able to limit to the minimum the risk of anybody intercepting and reading your relevant personal or business related documents.
- Avoiding monitoring – As we mentioned in #4, VPN pros can definitely help you if you happen to be exposed to increased censorship or monitoring. Having in mind that there are websites that know how to download various spyware and malware to computers, it is no wonder that so many people go for virtual private networks. After all, nobody would like to get their online activities monitored and their data potentially misused without them even knowing, right?
- Getting around regional content restrictions – Sometimes we end up not being capable of accessing specific types of video content in the region we are due to a request made by the original publisher. And it can feel quite annoying and discriminative. However, there is the possibility of making such restrictions disappear by using a VPN. So, keep that in mind.
Preventing Identity Threat
 It is often said how many risks and dangers are associated with hackers and other people with malicious intentions being able to access personal information. One of them relates to stealing someone’s identity during a bank account balance online check or when logging into a credit card site to make some monthly payment. It sounds horrifying, doesn’t it? Well, using VPN pros can help all of us feel safe and secure when dealing with transfers and information online.
It is often said how many risks and dangers are associated with hackers and other people with malicious intentions being able to access personal information. One of them relates to stealing someone’s identity during a bank account balance online check or when logging into a credit card site to make some monthly payment. It sounds horrifying, doesn’t it? Well, using VPN pros can help all of us feel safe and secure when dealing with transfers and information online.
Whether we are currently observed or not, it makes sense to keep in mind that it is no secret for anyone that there is such thing like governments’ electronic surveillance of citizens. For further information, check ECHELON. Look up Carnivore and its less threateningly named successor, DCS1000. So, there is no doubt whether such a monitoring technology exists. The only question that we still haven’t found a clear answer to is whether those communications are being collected and examined or not. And what is more, there are other parties who might be monitoring us this very second apart from the government. For instance, your ISP might be doing so in order to discount retailers.
All in all, even if it might not be so urgent to take these potential threats into consideration, do not neglect or underestimate them, neither. Despite the drawbacks of VPN-s, we cannot deny that they are a way of protecting yourself with the VPN pros. So, our purpose is to provide you with the necessary information about their role in today’s world, as well as to identify some of the market’s top subscription-based contenders. Hopefully, this will help you make up your mind by yourself from an informed point of view.
The Difference Between VPNs and VPN Proxy
It is not uncommon for people to mix the terms “VPN server” and “VPN proxy server” believing that they are about the very same thing. Despite the similarities between both of them, there are significant differences regarding functionalities. So, it is worth taking them into consideration if you aim at getting your needs met in the best possible way.
First, let us start by once again stating what VPN-s are about exactly. A virtual private network is a secure WAN (wide area network) which consists of a server and minimum one other endpoint. When it comes to the most frequently used protocols enabling VPN-s to serve as such a tunnel, we can list the following ones: PPTP, L2TP, IPSec, and SSL. Having in mind that the technology is still based on public Internet, there are still congestion and latency challenges that go hand in hand with it.
On the other hand, what VPN proxy servers do is enabling clients to request resources from servers. We can draw a parallel between proxy servers and the function of the Sigourney Weaver’s character in the movie Galaxy Quest. Her role included fielding information requests from the captain, conveying them to the ship’s computer system, as well as communicating back the answer once it was given by the machine. As far as real world computing is concerned, there is a client who needs some information from the end server. And because they are not situated in the very same location, it is only by using a proxy server as a way of preserving anonymity that the server can figure out what the request is about.
VPN Proxy Servers
 All in all, VPN proxy servers are nothing more than a tunnel for information to get transferred without any encryption while VPN pros ensure high privacy and protection as a result of the applied encryption. In addition to this, unlike VPN servers not every type of software is compatible with VPN proxy servers. So, if the software application enables using a proxy server as a forwarding arrangement, the chances are that you will easily get your request accepted, processed, sent as if it is made by the proxy server which is fine.
All in all, VPN proxy servers are nothing more than a tunnel for information to get transferred without any encryption while VPN pros ensure high privacy and protection as a result of the applied encryption. In addition to this, unlike VPN servers not every type of software is compatible with VPN proxy servers. So, if the software application enables using a proxy server as a forwarding arrangement, the chances are that you will easily get your request accepted, processed, sent as if it is made by the proxy server which is fine.
However, if it is necessary to make DNS requests appear as if they came from another country, there will be issues. Other challenges are related to games, VoIP, and other traffic types that might easily be processed if using a VPN. How come? Well, because of the fact that there is an adapter added to your computer which appears to be the primary one, all traffic is about to go out on the VPN to your end-point. This is how even DNS, gaming, and VoIP can easily be routed out via the network in a glimpse of an eye. What comes next is servers taking the traffic, anonymizing it and sending it to the end point. What a lovely way to ensuring that as a client you can relax without worrying about getting your IP address exposed. Security is definitely considered to be the very crucial point of differentiation when it comes to both services. In comparison to VPN proxy servers which are usually not encrypted, using VPN pros prevent your ISP from monitoring your traffic. As you can imagine, however, there are some drawbacks that go hand in hand with security. One of them has to do with the lower speed you need to cope with when you stream media or download files via a VPN server. And for us to be fully objective, we need to add that it VPN proxy servers are considered to enable IP masking for one single application or device in cases when VPN-s are not supported.
So, basically, there are various ways in which you can provide yourself with the ultimate privacy control and avoid accidental disconnects, as well as IP leaks. These options include VPN servers, VPN proxy servers and other techniques like layering.
To Trust or Not To Trust VPNs
When people consider using VPN services, they inevitably reach the point when they ask themselves whether it is wise to trust the VPN servers. After all, what is the benefit of general privacy and protection if VPN providers might end up forced to inform authorities about your identity and activities whenever they are demanded to?
According to Ted Kim from London Trust Media, they put significant efforts into making sure that all law enforcement requests are processed legally. Also, when it comes to Private Internet Access, he says, there is no information revealed neither about the user IP address nor anything else. The only thing is an email address thanks to which people get signed up. This means that even if service providers might have access to your specific IP address, Private Internet Access has found a way in which it is not possible to prove that a particular IP address has accessed another point through their network.
 When it comes to deanonymizing tools like the brouhaha, Ted Kim shares that despite the challenges that go hand in hand with it, it is not impossible to trace IP traffic. Still, the same logic applies for anonymizing oneself – as long as enough efforts and resources are deployed, it is not impossible to ensure it, neither.
When it comes to deanonymizing tools like the brouhaha, Ted Kim shares that despite the challenges that go hand in hand with it, it is not impossible to trace IP traffic. Still, the same logic applies for anonymizing oneself – as long as enough efforts and resources are deployed, it is not impossible to ensure it, neither.
When we talk about privacy, it is worth mentioning the standpoint of TorGuard CEO Ben Van Pelt, too. He shares that a lot of people find themselves mislead by the assumption that employing privacy definitely means that someone has something to hide. This might not necessarily be the case. According to Ben Van Pelt, privacy is just one of the main human rights. And it is quite an important one, isn’t it?
What to Consider When Purchasing a VPN
If you are about to purchase a VPN service, keep in mind that there are differences between the separate services, when we talk about VPN pros. Some of the main criteria you can have a look at when comparing paid and free options include advertising, performance, as well as privacy policies. In order for us to help you get an overview of the most relevant aspects to take into consideration in addition to the price, we have created a systemized list you can find bellow.
1. Personal Data Retention
This factor is often considered to be the most relevant one in the process of purchasing a VPN service. After all, why would you go for such a service if you cannot be fully anonymous? And this cannot happen given the fact that a VPN provider happens to log your identity and activities. If this is the case, make sure you are provided with adequate information related to assurances and details confirming that they neither monitor traffic nor record session activity or IP addresses. They shouldn’t capture timestamps, as well. Keeping no records can turn out to be very helpful if any authority demands from the respective provider to give such information about individual users.
2. Supported Client Diversity
It is important to check whether your devices and OS-es are covered. Despite the multiple apps that migrate to the cloud, there are still some types of software that run locally. VPN clients are considered to be one of them. So, check if there are Windows, Mac, Android, and iOS versions available. Also, make sure you research in advance if you happen to use Linux or other unconventional platforms like smart TVs and game consoles.
3. Total Number, Speed, and Location Of Servers
 In the case when there are no other differences between various providers and their VPN pros, some of servers can turn out to be a relevant criterion. The more of them there are, the better. After all, any user would like to benefit from as fast servers as possible that are closest to the client to minimize latency. It would also be good if you choose a provider with relatively low per-server load count. The reason for this has to do with the fact that the presence of fewer servers can result in congestion and paltry bandwidth allocation.
In the case when there are no other differences between various providers and their VPN pros, some of servers can turn out to be a relevant criterion. The more of them there are, the better. After all, any user would like to benefit from as fast servers as possible that are closest to the client to minimize latency. It would also be good if you choose a provider with relatively low per-server load count. The reason for this has to do with the fact that the presence of fewer servers can result in congestion and paltry bandwidth allocation.
What is also worth considering is that the bandwidth speeds offered by secondary market servers may be different from those in primarily developed nations. There will be various backbone and trunk speeds. So, do not make the mistake to purchase a subscription without having in mind your needs and having run some tests.
4. Supported Ciphers And Protocols
Whether you are aware of it or not, there are differences between the separate encryption methods (OpenVPN, AES-256-CBC, SHA3, etc.). So, keep in mind that there is a wide pool of ciphers to choose from when it comes to your connections. Therefore, you might be willing to inform yourself about your potential provider’s list of supported algorithms.
5. Embedded Anti-Malware
Being fully protected against monitoring and identity threats are essential as VPN pros. While you might already be used to running anti-malware software on all of your clients, you can benefit from additional security by running anti-malware scanning on the traffic of some providers.
6. Acceptable Payment Methods
To get the tracking credit cards are exposed to, you can use pre-paid cards. Doing so will make you provide more than just an email address as personal information, but still, it is not a big deal. Alternative methods include PayPal, Bitcoin, Plimus, and even cash. We also remind you of the fact that even if PCI (payment card industry) requirements do not allow the storing of payment data with customer records, providers are forced to come up with some way to record payments to user accounts for simple accounting. Despite this fact, there is no need to worry about it since you cannot understand what a user has done with a service by just knowing that he or she has purchased it.
7. VPN Location
How come that VPN servers can make it appear as if you are situated in another area than your actual one? Here is what the Digital Community Team of IPVanish has to share about it. According to them, it is third-party entities that help websites find out the location of their visitors (geolocation). So, what happens is that the website provider pays for gaining access to a database with the most recent information. This is how the IP address of every visitor gets checked based on the information in the database and voila. Location pops up. However, it is also true that there is no legal requirement preventing geolocation companies from providing misleading information about the site. And VPN servers benefit from that.
 In addition to this, it is not uncommon for owners of websites to buy a copy of the database and to not pay for updates of the VPN pros later on. As you can imagine, this can result in differences related to the content of both sources later on.
In addition to this, it is not uncommon for owners of websites to buy a copy of the database and to not pay for updates of the VPN pros later on. As you can imagine, this can result in differences related to the content of both sources later on.
Also, keep in mind that the majority of geolocation providers check the IPs, which frequently access a server with their database, by using crawlers. After that, they refer that information to what they know has been accessed so that they can identify the location. So, it is no wonder that in the cases when there is a lot of conflicting data providers are likely to put the IP address in the middle of the ocean and call it a day or they might also correlate it to the biggest similarity and figure out the respective location as a result of this.
What we need to get clarity about has to do with the situations when we physically provide ourselves with a server which is located elsewhere, regardless of which there are people who are not willing to report it precisely. It is not uncommon for affected providers to request corrections related to this. So, it is worth taking these aspects into consideration.
Conclusion
Here we are at the end of our overview of the VPN pros and cons as well as the VPN proxy. We hope that you have found useful answers to all burning questions regarding VPN and VPN proxy servers so that now you are capable of making an informed decision about the most suitable way of protecting your privacy when being online.
Helpful Links
- SSH-Based Virtual Private Networks (Open BSD Manual Pages)
- Unix Toolbox Section on SSH-VPN (Single or Two Networks)